Building Education-Employment Pathways That Enable Equitable Economic Mobility
Read CAEL's latest report: How They Pay: The Voices of Adult Learners on College Affordability, and How Institutions Are Responding
Read More →

CAEL Awarded $1.4 million U.S. Department of Agriculture SNAP Employment and Training National Partnership Grant
Read More →

CAEL Receives $15.7 Million Grant From Truist Foundation to Strengthen Financial Services Career Pathways
Read More →
New Research from CAEL and a New Framework for Creating Adult Learner Leaders for Institutional Effectiveness (ALLIES)
Read More →

This year CAEL is celebrating our 50th anniversary in New Orleans at the 2024 CAEL Conference, scheduled from October 30th to November 1st!
Read More →

The National Association of Workforce Boards (NAWB) and CAEL are joining forces to launch the Advancing Equity initiative and the Advancing Equity Leadership Academy.
Read More →
2022 CAEL Impact Report
Welcome to CAEL’s inaugural impact report, which provides examples of how our work over the previous 12 months made a positive difference for the communities we serve. Each of the achievements you read about in this report is both a reason to celebrate our progress and a reminder that meeting adult learners where they are is a journey that never ends.
Championing Adult Learners
Nearly 90 million workers in the U.S. lack the skills needed to thrive in the future workforce. That’s not too surprising when we consider that among adults (25+) in 2022, 84 million had a high school diploma or less, 33 million had completed some college, and 77 million had college degrees. Further, 80 percent of workers say their college education was not relevant to their field.*
For such workers, closing skills gaps means finally crossing the divide between their low-wage job to more rewarding work. And thousands of employers CAEL works with show that opportunities for career advancement come along with further skill development and credentials that increase earnings. That’s why adult learners and workers expect education and training to position them for advancement along rewarding career pathways. From apprenticeships to advanced degrees, the choices can be overwhelming. But the success of educators, employers, and entire communities depends on empowering adult learners to make the right choices. CAEL positions our stakeholders to do just that.
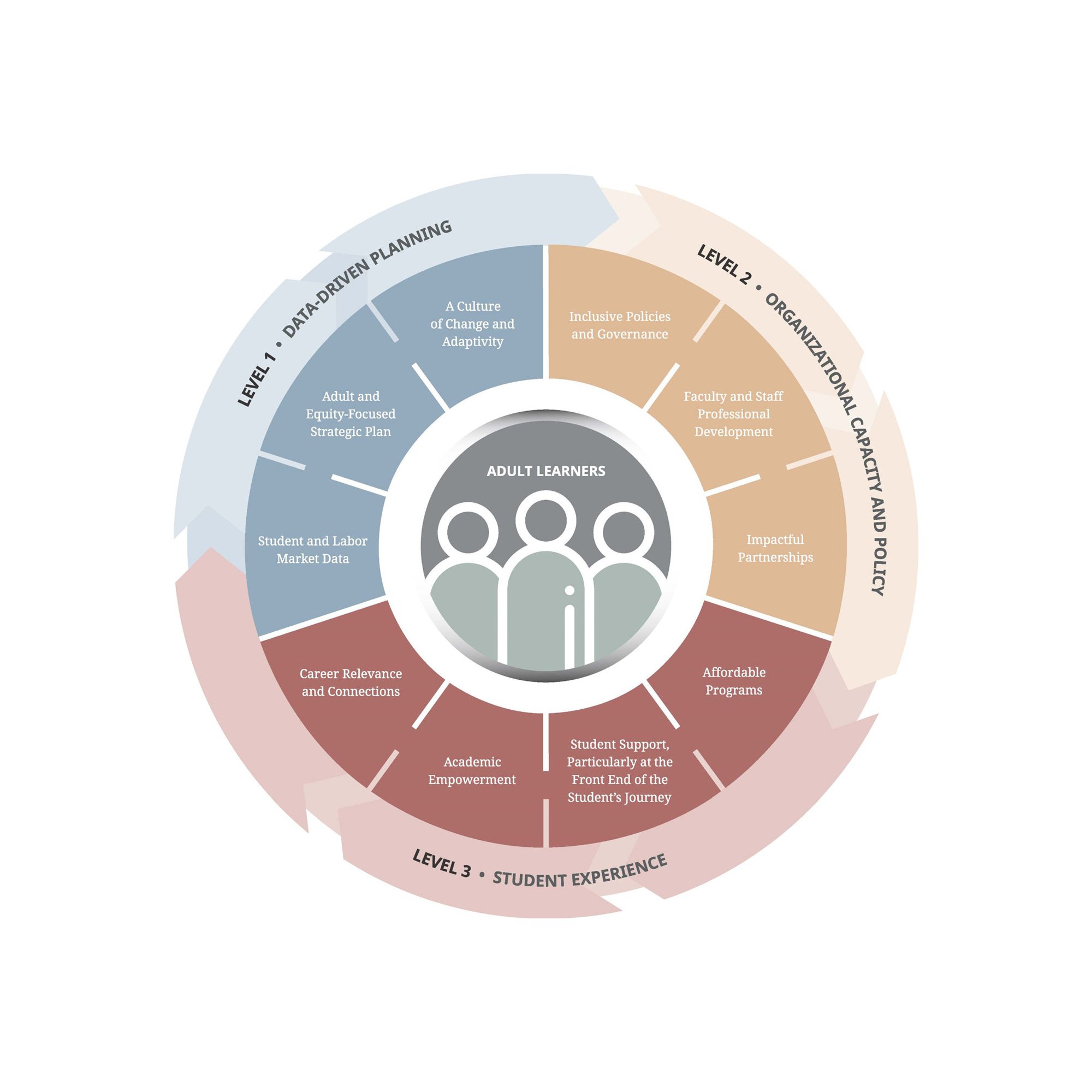
CAEL (Council for Adult and Experiential Learning) has found that adult learners and workers can only realize their potential within a well-aligned industry, education, and workforce ecosystem. We help build organizational partnerships that center adult learners and workers in initiatives that span the continuum from education to employment. These include workforce and economic developers; chambers of commerce, postsecondary educators; employers and industry groups; and foundations and other mission-aligned organizations. If you are in one of these groups, we can help you meet adult learners and workers where they are and benefit the ecosystem and help achieve your goals by partnering on pathways that support equitable economic mobility and helping adult learners and workers navigate them.
*Source: Table 2. Educational Attainment of the Population 25 Years and Over, by Selected Characteristics (https://www.census.gov/data/tables/2022/demo/educational-attainment/cps-detailed-tables.html)
Key Current Initiatives
Advancing Delta Talent Initiative
SNAP Employment & Training
Truist Foundation - Build Better Careers
The impact of adult learning is felt across lifetimes.
Overall Reach
The Value of CAEL Membership



The Value of CAEL Membership


University of Memphis




Explore the Most Recent News from CAEL

How the Evolution of Microcredentials Is Meeting the Needs of an Evolving Industry